Why ChatGPT Is Obsessed With Goblins: The Weirdest Possible ExplanationApr 30
openai said the latest models developed a "creature language" quirk — but not why they fixated on goblins *specifically*
Dec 16, 2022
Twitter’s power users in the media and commentariat have been pathologically obsessed with Elon Musk’s acquisition of the platform since April. For his part, Musk has been happy to add fuel to the fire by providing several independent journalists with the Twitter Files, which exposed the activist nature of the company’s content moderation during the 2020 presidential election cycle. But back in July, well before the Musk/Twitter discourse went nuclear, Twitter’s former head of security released a shocking whistleblower report alleging, among other things:
that agents of foreign governments such as those of China and India had infiltrated the company and were on its payroll
that Twitter’s security systems were egregiously porous and could have allowed external organizations and foreign governments to monitor employee laptops and steal user data such as physical location of last login, phone number, etc.
that its database architecture was so flimsy that Twitter nearly permanently collapsed in the spring of 2021
that Twitter’s laughably poor management of user data prevented the company from even detecting, identifying, and resolving security breaches when they happened
and that company executives, particularly Parag Agrawal, preferred to lie about all these problems, rather than fix them
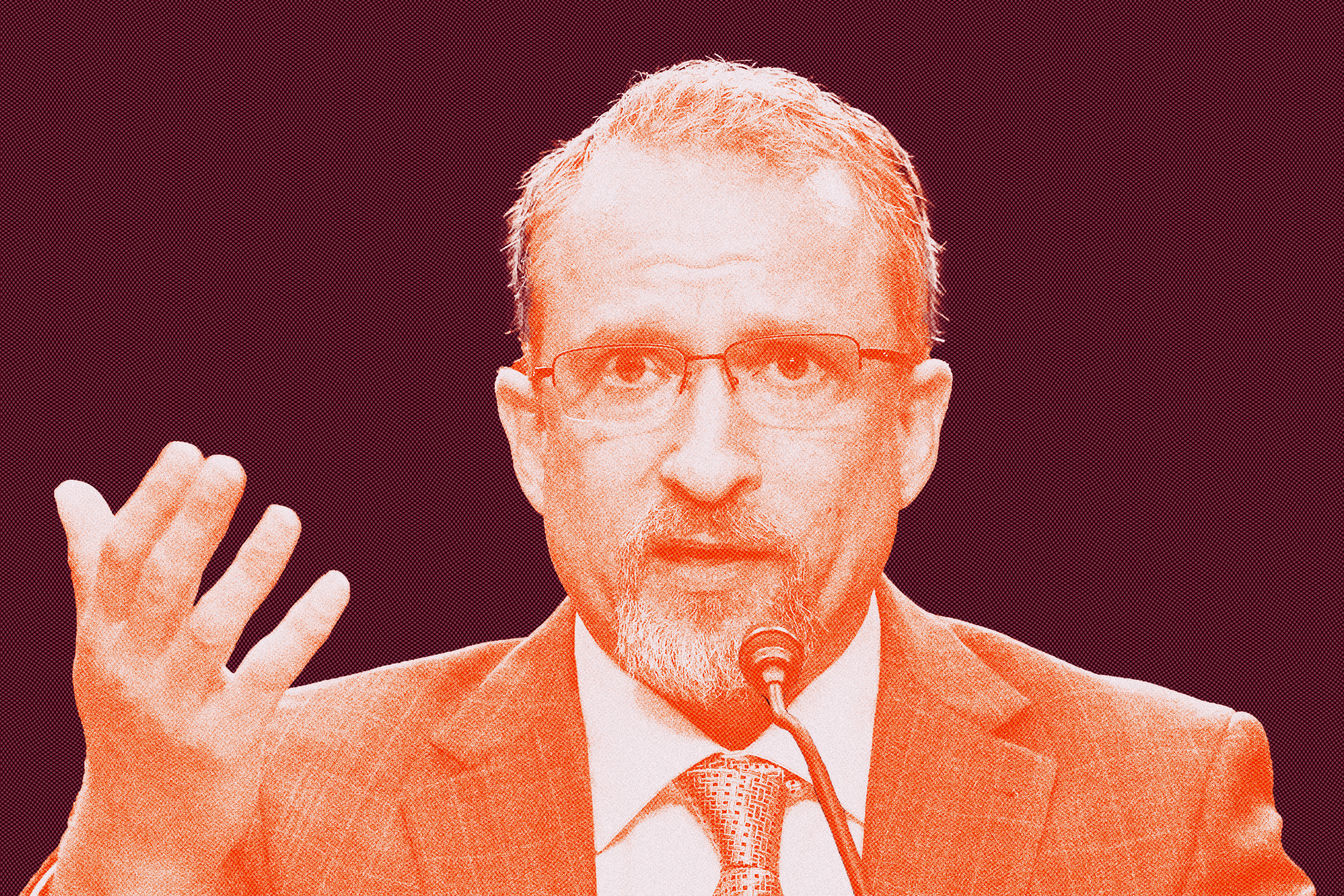
But compared to the discourse around Musk’s acquisition and The Twitter Files, the whistleblower report fell completely flat on media Twitter when it was published, and has received little attention in the narrative since. This couldn’t be because of the whistleblower’s lack of credibility: Peiter “Mudge” Zatko was a cybersecurity pioneer in the internet’s early days, and his pre-Twitter resume includes stints at Google, Stripe, and DARPA. Maybe the report’s allegations simply added up to a nothingburger? Not the case either—Mudge’s claims prompted a Congressional testimony, where he painted a picture of a company endlessly plagued by serious security issues and data breaches, exacerbated by an effete executive team that repeatedly denied, misdirected, and downplayed the extent of the problems. Let’s take a look.
